Why Quantum Computers Need 1,000 Qubits for One
TL;DR: Hardware random number generators harvest quantum and thermal noise from silicon to produce the unpredictable bits that secure every encrypted connection. This article traces the physics, engineering, standards, and controversies behind the invisible entropy engines powering modern cryptography.
Every time you open a banking app, send an encrypted message, or connect to a website over HTTPS, your device needs something no algorithm can truly provide: genuine randomness. Not the kind of randomness a clever formula spits out, but the deep, irreducible unpredictability baked into the fabric of physics itself. Somewhere inside your processor, electrons are tunneling through barriers they shouldn't be able to cross, and that quantum weirdness is what stands between your data and anyone who wants to steal it.
This is the story of hardware random number generators, the invisible engines that harvest chaos from the subatomic world and turn it into the cryptographic keys protecting modern civilization.
Here's the uncomfortable truth about pseudorandom number generators (PRNGs): they're deterministic. Give a PRNG the same seed, and it will produce the exact same sequence of numbers every single time. For simulations and games, that's fine. For cryptography, it's a disaster waiting to happen.
The problem isn't that PRNGs produce bad-looking numbers. Modern cryptographically secure PRNGs like ChaCha20 generate output that passes every statistical test you can throw at it. The problem is that if an attacker discovers or guesses the seed, every "random" key, nonce, and initialization vector your system ever generated becomes predictable. The entire security model collapses.
True random number generators (TRNGs) solve this by tapping into physical processes that are fundamentally unpredictable. Not unpredictable because they're complicated, but unpredictable because the laws of physics say so. Quantum mechanics doesn't just make prediction difficult, it makes prediction provably impossible at the most fundamental level.
This distinction matters more than most developers realize. When you call a cryptographic API to generate a TLS session key, the quality of that key depends entirely on the entropy source feeding it. Software alone can stretch and redistribute randomness, but it cannot create it from nothing.
If an attacker can predict your random number generator's output, every cryptographic key your system has ever produced is compromised. True randomness isn't a nice-to-have. It's the foundation everything else is built on.
Two families of physical phenomena power most hardware RNGs on the market today, and both trace back to fundamental physics that's been understood for roughly a century.
Every resistor in every circuit generates a tiny, random voltage fluctuation called Johnson-Nyquist noise. This noise arises because electrons in a conductor are in constant thermal motion, bouncing around with energies determined by temperature. The power of this noise follows the formula P = 4kTBR, where k is Boltzmann's constant, T is temperature in Kelvin, B is the measurement bandwidth, and R is resistance.
What makes thermal noise useful for cryptography is that it's fundamentally stochastic. Even if you knew the exact temperature, resistance, and bandwidth, you couldn't predict the instantaneous voltage at any given moment. The randomness is intrinsic to statistical mechanics itself.
Deeper still, quantum mechanics provides entropy sources that are random by the very nature of reality. In a Zener diode operating in reverse breakdown, electrons quantum-tunnel through a potential barrier. The probability of any individual electron tunneling decreases exponentially with barrier width, but whether a specific electron tunnels at a specific instant is genuinely indeterminate. No hidden variable, no deeper pattern, just pure quantum probability.
Shot noise provides another quantum entropy source. When current flows through a semiconductor junction, it arrives as discrete electrons, and the statistical fluctuation in their arrival times follows the Schottky formula: the variance equals 2qI, where q is the electron charge and I is the average current. Each electron's arrival is an independent quantum event.
Ring oscillators offer yet another approach, particularly popular in FPGA implementations and ARM processors. Two free-running oscillators accumulate phase jitter from thermal and quantum effects, and the jitter between them provides entropy. ARM's TrustZone CryptoCell uses exactly this technique, sampling the jitter between ring oscillators to feed its on-chip TRNG.
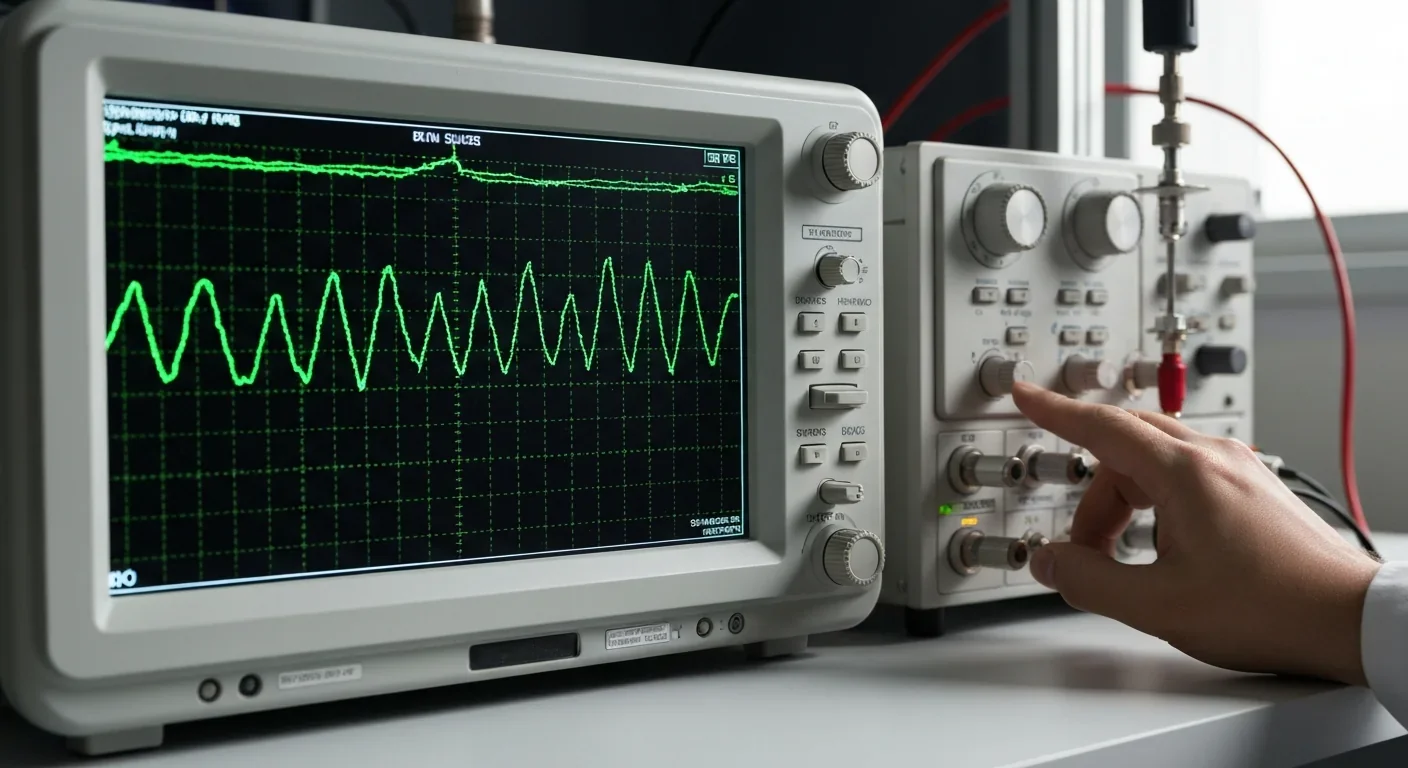
Raw physical noise is messy. It's biased, correlated, and riddled with the fingerprints of the analog circuit that captured it. Turning that raw entropy into uniform, independent random bits requires a carefully engineered pipeline.
First, the analog noise signal passes through a comparator or analog-to-digital converter. A simple approach samples the noise voltage at regular intervals and outputs a 1 if it's above a threshold or a 0 if it's below. But these raw bits are never perfectly uniform, because real circuits have offsets, drift, and environmental sensitivity.
This is where cryptographic conditioning steps in. Intel's RDRAND, for example, feeds raw thermal noise through an AES-CBC-MAC conditioner that cryptographically mixes the input to produce near-uniform output. The conditioner acts as an entropy extractor: it takes a stream with, say, 0.8 bits of entropy per raw bit and concentrates it into output where each bit carries essentially 1 full bit of entropy.

Other approaches include von Neumann debiasing (which pairs consecutive bits and discards matching pairs), cryptographic hash extraction, and XOR-based schemes. Each trades throughput for uniformity, and the choice depends on the application's speed and security requirements.
The most paranoid part of the pipeline, and arguably the most important, is continuous health testing. NIST SP 800-90B mandates two specific tests that run constantly: the repetition count test, which catches sequences of identical outputs that are too long, and the adaptive proportion test, which detects statistical shifts in the output distribution.
These tests exist because hardware can fail silently. A TRNG's entropy source can degrade from temperature drift, voltage fluctuation, aging components, electromagnetic interference, or even deliberate tampering. Without continuous monitoring, a broken RNG looks identical to a working one from the outside.
"NIST SP 800-90B requires just two continuous health tests: the repetition count test and the adaptive proportion test, ensuring that entropy sources are monitored at every point in their operation."
- NIST SP 800-90B, Recommendation for Entropy Sources Used for Random Bit Generation
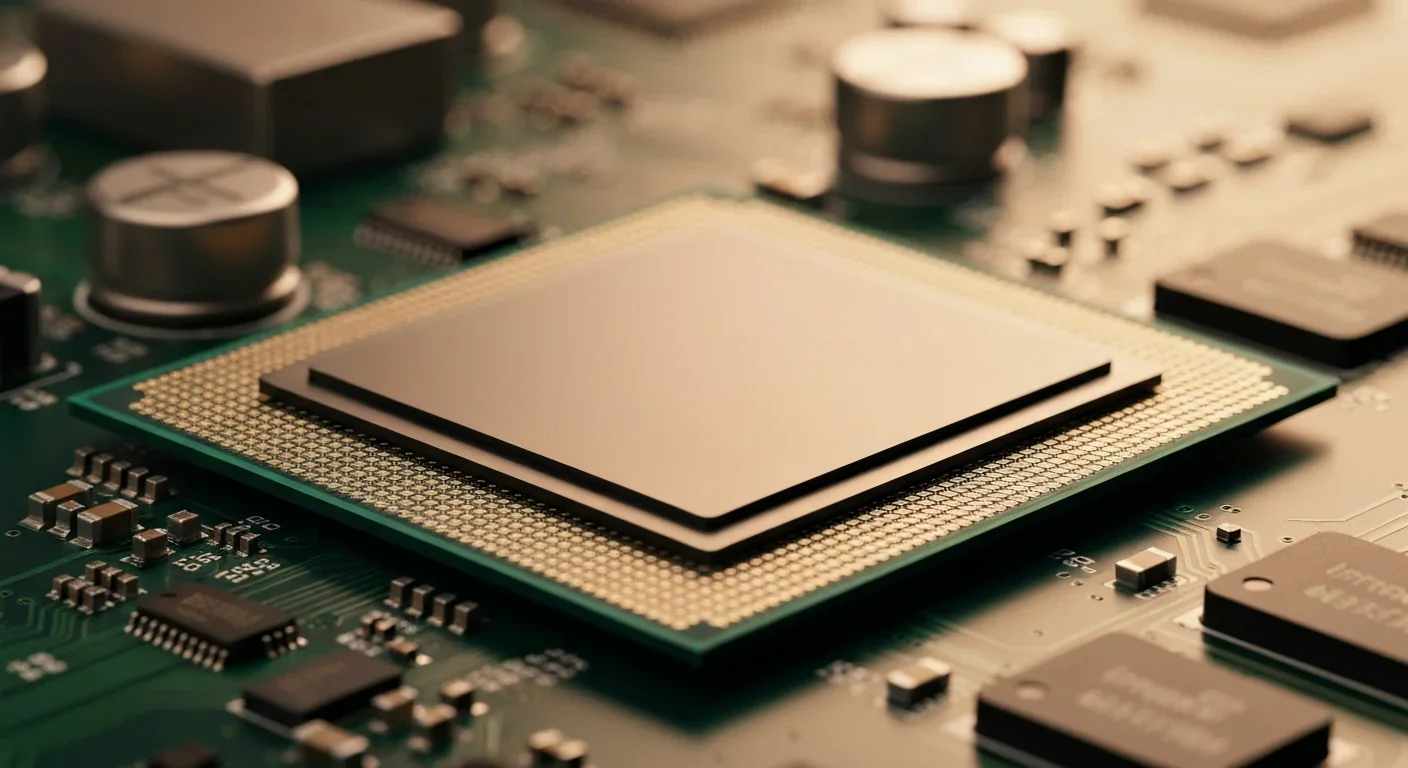
Intel introduced the RDRAND instruction with Ivy Bridge processors in 2012, making hardware entropy available to every program through a single CPU instruction. The on-chip entropy source uses thermal noise from a circuit designed specifically for randomness harvesting. That noise feeds into the AES-CBC-MAC conditioner, which outputs 128-bit random blocks. RDSEED, introduced later, provides direct access to 256-bit conditioned entropy samples intended for seeding software CSPRNGs.
One practical detail that matters: RDRAND sets the carry flag to indicate success or failure. If the internal entropy pool is exhausted or a health test fails, the carry flag reads zero, and the caller must retry. This is a critical check that software developers sometimes skip, to their peril.

The Linux kernel integrates RDRAND into its entropy infrastructure through a mixing approach. The kernel's random subsystem XORs RDRAND output with other entropy sources, so even if RDRAND were compromised, the mix would be no worse than the other sources alone. Since kernel 5.6 in 2020, Linux's /dev/urandom uses ChaCha20 as its CSPRNG, seeded from this blended entropy pool. The rngd daemon actively feeds additional hardware entropy into the pool during runtime.
ARM's TrustZone CryptoCell provides TRNG capabilities based on ring oscillator jitter, making hardware entropy available across the massive ARM ecosystem, from smartphones to IoT sensors. For resource-constrained devices like the ESP32, entropy harvesting gets creative. The ESP32's bootloader collects entropy from active Wi-Fi and Bluetooth radios during boot to seed its TRNG, since the radio frequency noise provides a convenient physical entropy source.
For IoT devices without their own capable TRNGs, recent research has explored supplying external entropy to RISC-V trusted execution environments, acknowledging that not every embedded chip can harvest sufficient entropy on its own.
In 2013, the Snowden leaks ignited a firestorm around hardware RNG trust. Revelations that the NSA had influenced the Dual_EC_DRBG standard, deliberately inserting a backdoor into a NIST-approved random number generator, raised an obvious question: could Intel's RDRAND be similarly compromised?
The concern was legitimate. RDRAND is a black box on silicon. You feed it a request, and it returns random-looking bits, but there's no way for an external observer to verify that the entropy source is genuine and uncompromised. A subtle bias or a hidden deterministic pattern could weaken every key generated on affected hardware, and nobody outside Intel would know.
The Linux kernel never relies on RDRAND alone. It XORs hardware entropy with environmental noise, timing jitter, and other sources, so a compromised chip can't silently undermine the system's randomness.
The Linux kernel community took this seriously. Linus Torvalds and other developers ensured that RDRAND was never the sole entropy source for /dev/random or /dev/urandom. Instead, it's mixed with environmental noise, timing jitter, and other inputs. This defense-in-depth approach means that a compromised RDRAND would need to be paired with compromises in every other entropy source to break the system.
The broader lesson applies beyond Intel. Public disclosure of entropy extraction algorithms and conditioning logic helps mitigate the black-box risk. Open designs that can be independently audited provide far stronger assurance than any proprietary claim of security. Germany's BSI agency classifies random number generators under AIS 31, with the P2 category requiring a mathematical proof of entropy, not just statistical testing.
NIST's SP 800-90 series provides the regulatory backbone for random number generation in the United States and, by extension, much of the world. SP 800-90A covers deterministic random bit generators (the CSPRNG layer). SP 800-90B specifies entropy source requirements. And SP 800-90C defines how to combine them into complete Random Bit Generator constructions, organized into four classes: RBG1, RBG2, RBG3, and RBGC.
Manufacturers seeking FIPS 140-3 certification must demonstrate that their entropy sources meet SP 800-90B through NIST's Entropy Source Validation Test Server. This involves submitting raw noise samples, restart test data, and detailed documentation of the entropy source design. The requirements are considerably more comprehensive than what FIPS 140-2 demanded, reflecting hard-won lessons about what can go wrong when entropy validation is treated as an afterthought.
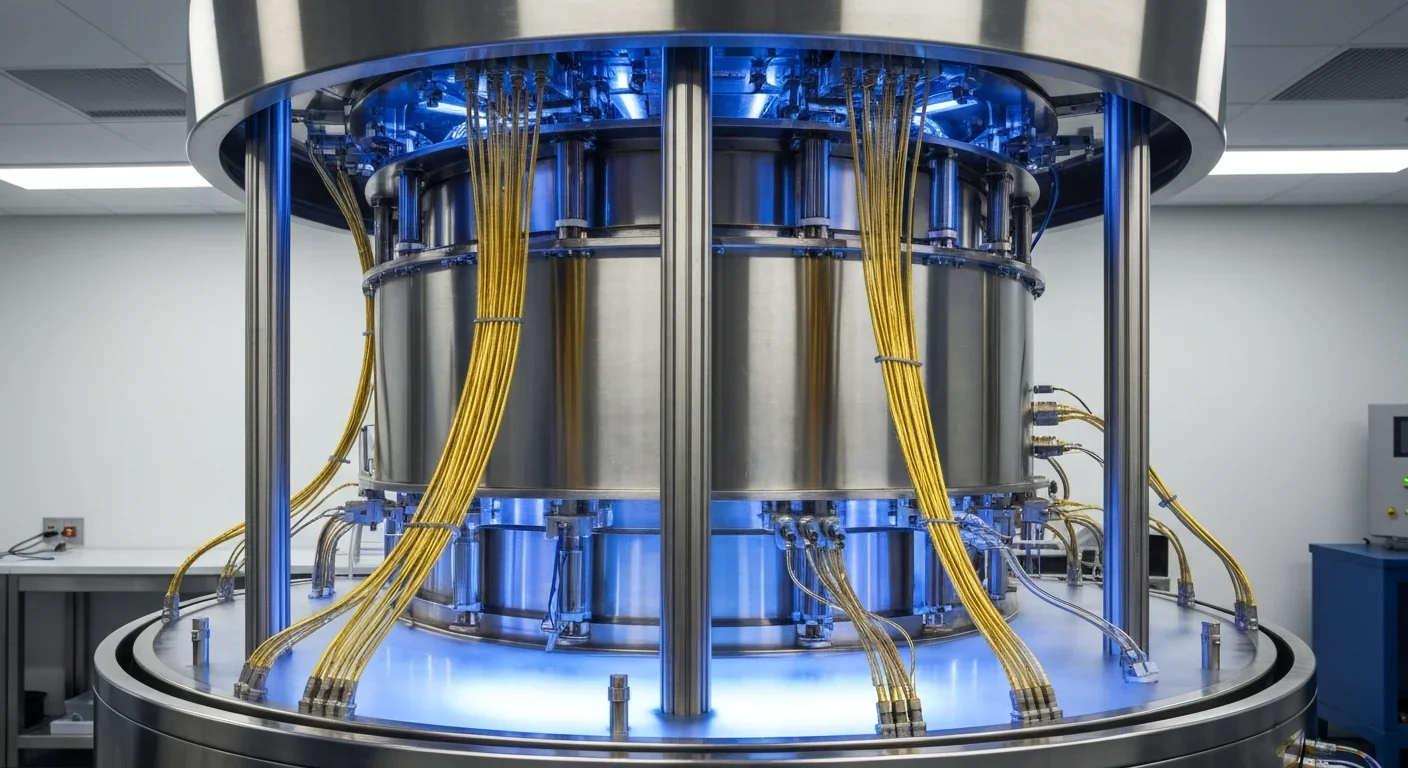
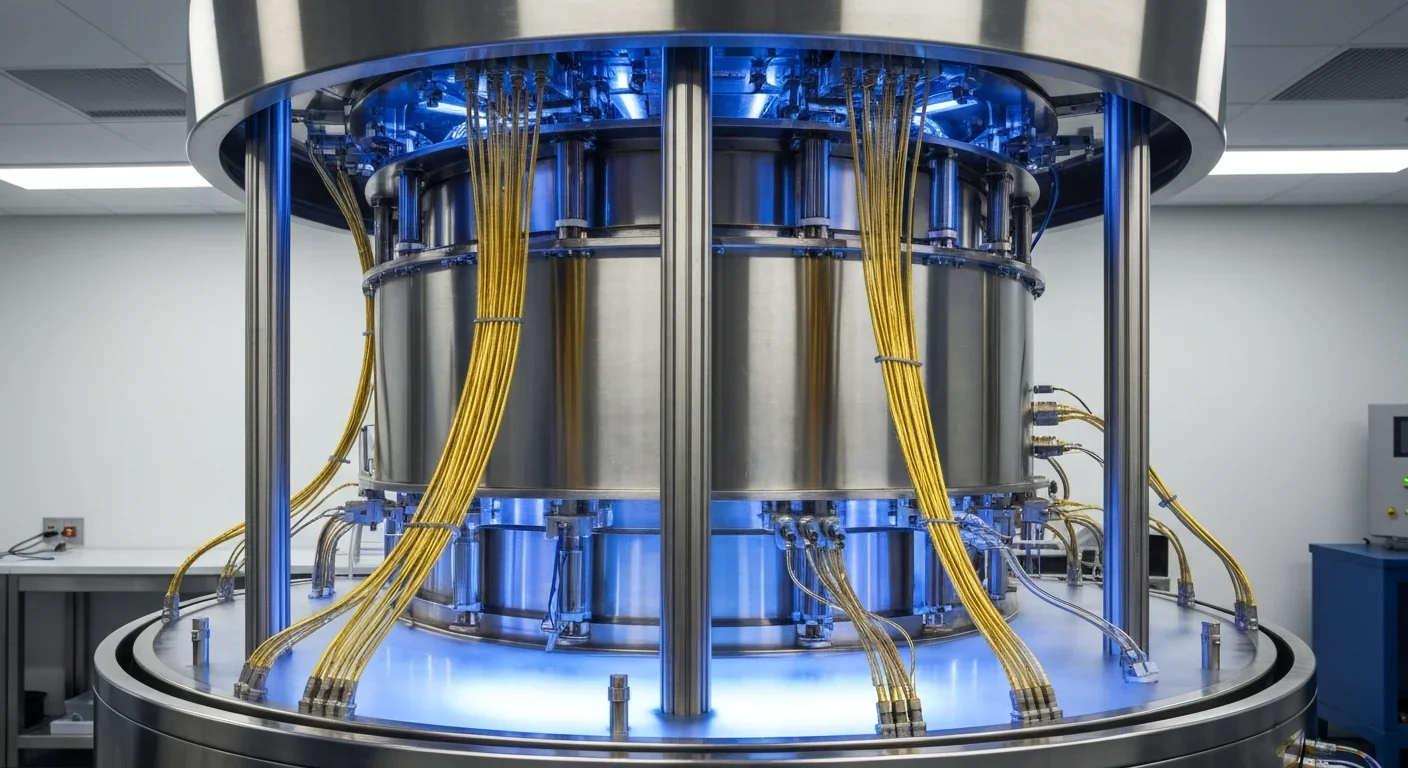
Classical HRNGs rely on physical processes that are random in practice. QRNGs go further, exploiting quantum phenomena where randomness is guaranteed by the laws of quantum mechanics, not just by our inability to measure precisely enough.
ID Quantique, a Swiss company that has pioneered commercial QRNGs since 2001, builds devices that generate random numbers by detecting individual photons. Their Quantis QRNG PCIe card achieves 240 Mbps of entropy in continuous mode, with AIS-31 P2 certification earned in collaboration with German research labs. Their Quantis Appliance can deliver 8,000 parallel 256-bit key requests per second, targeting data center workloads.
"The chip uses an on-chip optical amplifier and a second photodiode to suppress crosstalk, enabling a 3 Gbps random number output with minimal post-processing."
- Optica, reporting on next-generation QRNG research
The QRNG market is growing rapidly, driven by the approaching quantum computing threat to current encryption. In December 2024, Synergy Quantum deployed a QRNG at the Centre for Development of Advanced Computing in India. In January 2025, Palo Alto Networks launched a quantum random number generator open API framework, making quantum entropy accessible through standardized interfaces.
Recent hardware advances are impressive. Researchers demonstrated a QRNG that outputs 3 Gbps of random data using an on-chip optical amplifier and dual photodiode architecture for noise rejection, running continuously for 24 hours without degradation. Meanwhile, Thales Luna T-Series HSMs now embed FIPS 140-2 compliant QRNG chips directly into their hardware security modules.
Perhaps the most telling sign that QRNGs are leaving the lab: ID Quantique's QRNG chip has been integrated into a consumer smartphone, the Vsmart Aris 5G made by VinSmart.
If you're writing software that calls cryptographic APIs, here's what you should take from all of this.
First, never assume your entropy source is working. Check return codes. If you use RDRAND directly, verify the carry flag. If you use /dev/urandom, understand that early-boot entropy may be limited before the system has gathered enough environmental noise.
Second, defense in depth matters. The Linux kernel's approach of mixing multiple entropy sources is the gold standard. Don't rely on any single source, however trustworthy it appears.
Third, understand that HRNG quality is measurable. Tools exist to evaluate Shannon entropy, min-entropy, chi-square distribution, and NIST test pass rates. If your application demands high assurance, test your entropy.
The next decade will likely see QRNG chips become as standard as Wi-Fi modules in computing hardware. As post-quantum cryptography standards roll out, the demand for high-throughput, provably random entropy will only grow. The invisible physics that powers every encrypted connection today is about to get a quantum upgrade, and the security of everything we build will depend on getting it right.

Saturn's moon Titan may harbour liquid water beneath its frozen crust, kept from freezing by ammonia acting as a natural antifreeze. New Cassini data suggests the interior could be slush with warm water pockets rather than a global ocean, and NASA's Dragonfly mission launching in 2028 aims to investigate whether this exotic environment could support life.

Bacteroides thetaiotaomicron uses 88 specialized gene clusters and over 260 enzymes to decode and digest dietary fibers humans can't break down, converting them into essential short-chain fatty acids. When fiber runs out, it eats your gut's protective mucus instead, with cascading health consequences.

Scientists are restoring Ice Age ecological dynamics through rewilding projects like Siberia's Pleistocene Park and de-extinction efforts by Colossal Biosciences. These initiatives aim to reintroduce megafauna or their proxies to repair broken ecosystems, protect Arctic permafrost, and slow climate change.

The cheerleader effect is a proven cognitive bias where people look more attractive in groups because the brain automatically averages faces, smoothing out individual flaws. Research shows the sweet spot is 3-5 people, it works for all genders, and it has real implications for dating apps and social media strategy.

The Hawaiian bobtail squid farms bioluminescent bacteria in a specialized light organ to erase its shadow in moonlit waters. This partnership, where bacteria reshape the squid's body and communicate through quorum sensing, is teaching scientists how host-microbe relationships work and inspiring new medical and biotech applications.

Millions are leaving social media platforms driven by privacy scandals, mental health concerns, and algorithmic manipulation. While 60% relapse within a week, those who stay away report dramatically improved wellbeing, and decentralized alternatives like Bluesky are surging.
Building a reliable quantum computer requires roughly 1,000 fragile physical qubits per logical qubit due to surface code error correction overhead. New code families like LDPC and neutral-atom platforms are racing to slash that ratio, with some teams claiming it could drop to as few as 5-to-1.